Difference between revisions of "ISSS608 2017-18 T3 Assign Aakanksha Kumari Data Preparation"
Jump to navigation
Jump to search
| Line 70: | Line 70: | ||
* Gephi for Network Visualization | * Gephi for Network Visualization | ||
* Tableau Desktop for Visualization </big> </div> | * Tableau Desktop for Visualization </big> </div> | ||
| + | |} | ||
| + | |||
| + | |||
| + | == '''Data Prep''' == | ||
| + | |||
| + | {| class="wikitable" | ||
| + | |- | ||
| + | | <div style="font-family:Palatino Linotype; border-radius: 1px "> <big> | ||
| + | Converting the Time in all the CSV’s from seconds to the standard format and baselining the time w.r.t May 11, 2015 at 14:00. | ||
| + | Using Python datetime and panda’s library the modification was done. | ||
| + | </big> </div> | ||
|} | |} | ||
Revision as of 23:46, 7 July 2018
MC Challenge 3
|
|
|
|
|
|
|
|
|
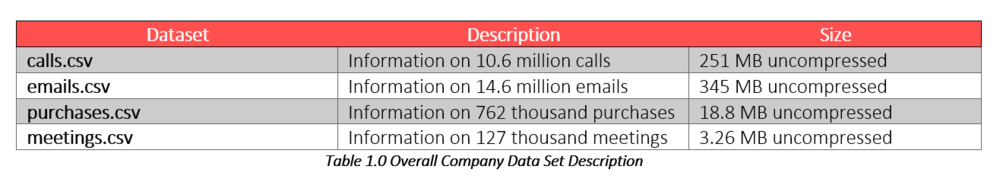
Data Set
The Kasios Insider has provided data from across the company. There are call records, emails, purchases, and meetings. The data only includes the source of each transaction, the recipient (destination), and the time of the transaction. Contents of emails or phone calls are not available.
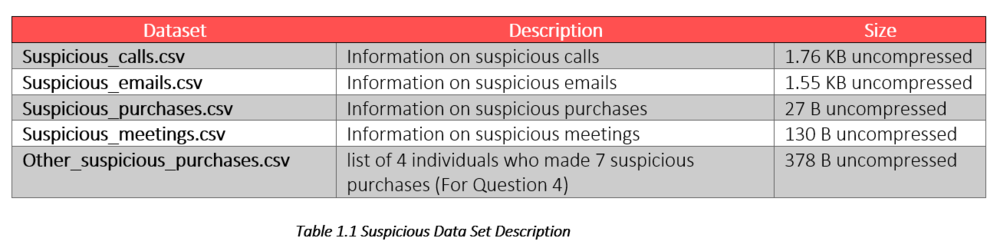
There are four data files that contain information about individuals that the Insider has indicated as suspicious:
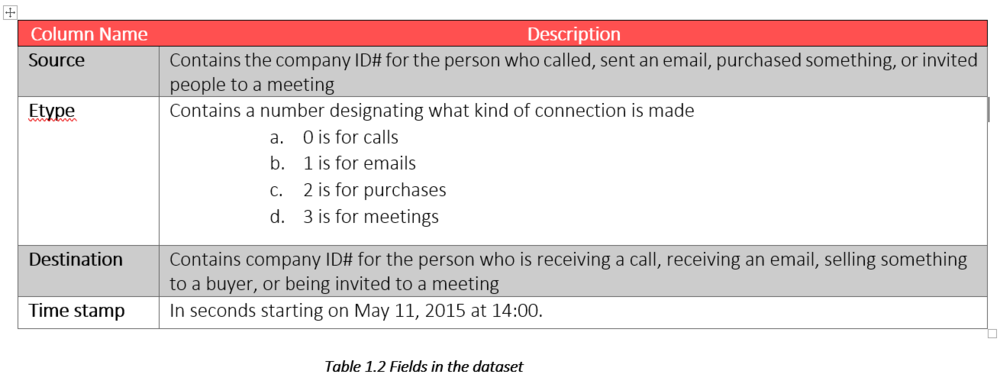
All provided data files have the same format. The data are provided in comma-separated format with four columns:
|
Tools
|
Data Prep
Converting the Time in all the CSV’s from seconds to the standard format and baselining the time w.r.t May 11, 2015 at 14:00. Using Python datetime and panda’s library the modification was done. |