Difference between revisions of "ISSS608 2017-18 T3 Assign Yu Zhecheng Insight"
| (15 intermediate revisions by the same user not shown) | |||
| Line 69: | Line 69: | ||
<tr> | <tr> | ||
<td><b> 1. Explore the company </b> | <td><b> 1. Explore the company </b> | ||
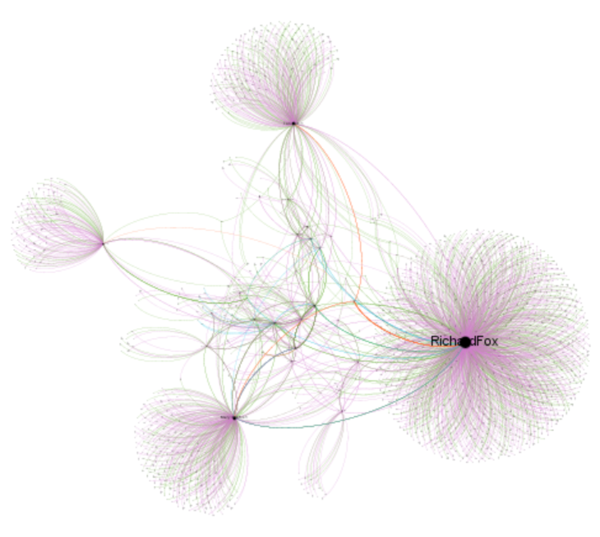
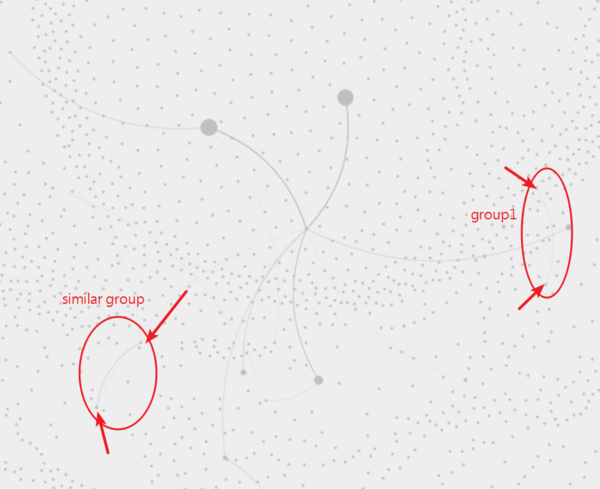
| + | <br>The node of first network graph is node.csv and the edge is egde.csv. Layout ''YIFAN HU''was selected. The color represents different attributes. | ||
| + | <br>'''Green:calls''' | ||
| + | <br>'''Orange:Purchases''' | ||
| + | <br>'''Blue:Meetings''' | ||
| + | <br>'''purple:emails''' | ||
| + | <br>It's quite clear that there are some clusters in the graph. | ||
| + | </td> | ||
| + | <td>[[File:YzcSus7.png|600px|center]]</td> | ||
| + | </tr> | ||
| + | <tr> | ||
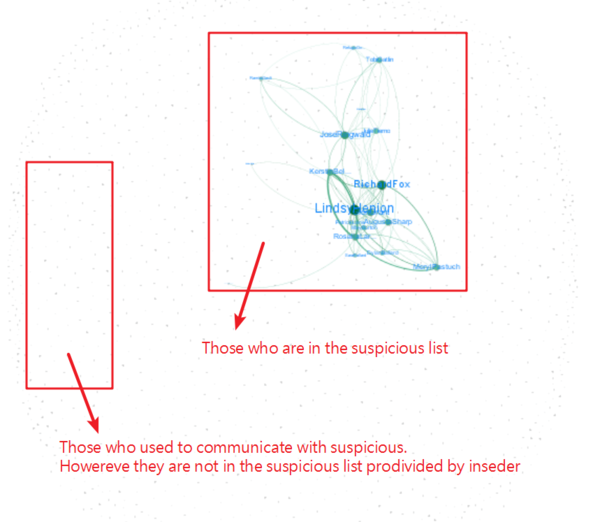
| + | <td><b> 2. Explore the company(2)</b> | ||
<br>To locate the suspicious in the larger group,I set node.csv as node which represent all people who used to communicate with suspicious from 2015 to 2017. On the other hand, I regard sus.csv as edge,which represent suspicious file provided by insider. '''It's easy to find out where the suspicious are. Although the file didn't tell us any details about the employee. I can speculate what status they are according to the number of emails,calls,meetings and purchases the employ is recorded.''' For example, those who received most emails in a year should be a management. | <br>To locate the suspicious in the larger group,I set node.csv as node which represent all people who used to communicate with suspicious from 2015 to 2017. On the other hand, I regard sus.csv as edge,which represent suspicious file provided by insider. '''It's easy to find out where the suspicious are. Although the file didn't tell us any details about the employee. I can speculate what status they are according to the number of emails,calls,meetings and purchases the employ is recorded.''' For example, those who received most emails in a year should be a management. | ||
| + | <br>'''Layout ''Fruchterman Reingold'''was selected. | ||
</td> | </td> | ||
<td>[[File:YzcSus1.png|600px|center]]</td> | <td>[[File:YzcSus1.png|600px|center]]</td> | ||
| + | </tr> | ||
| + | <tr> | ||
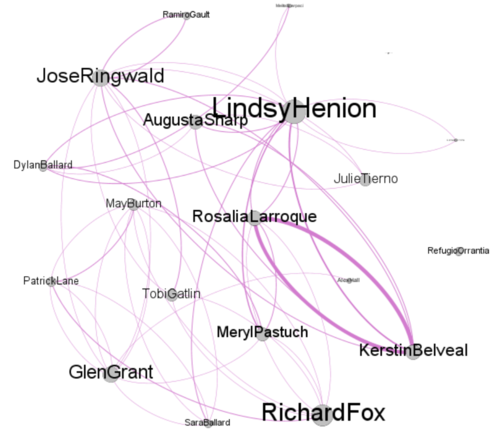
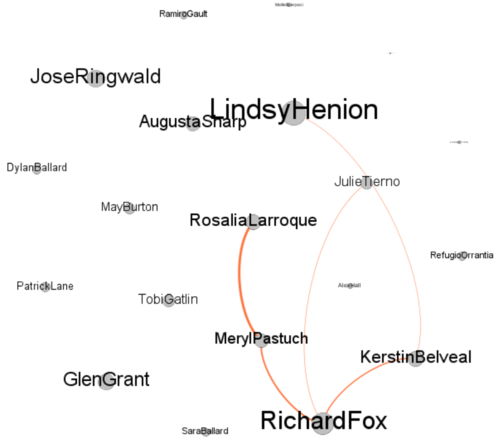
| + | <td><b> 3. Explore the company(3) </b> | ||
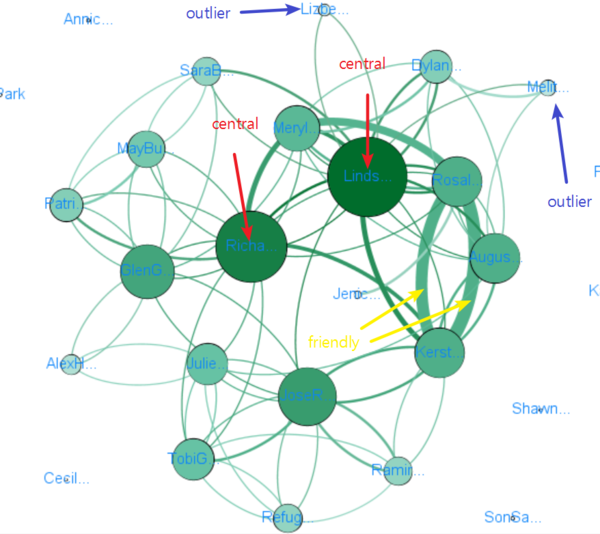
| + | <br>Bigger size of points indicate how important they are in the suspicious group. It's easy to find out that ''Linds'' and ''Richa'' might be the important guys in the group. Furthermore, it's quite interesting to find that there are some outliers in the network. They are far from the central and the size of the point is quite small. It means that they only communicate with suspicious few time. | ||
| + | </td> | ||
| + | <td>[[File:YzcSus2.png|600px|center]]</td> | ||
| + | </tr> | ||
| + | <tr> | ||
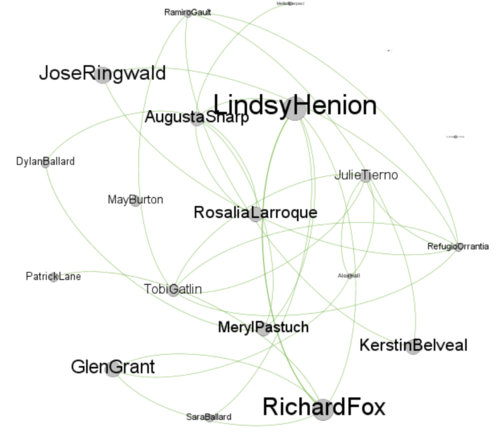
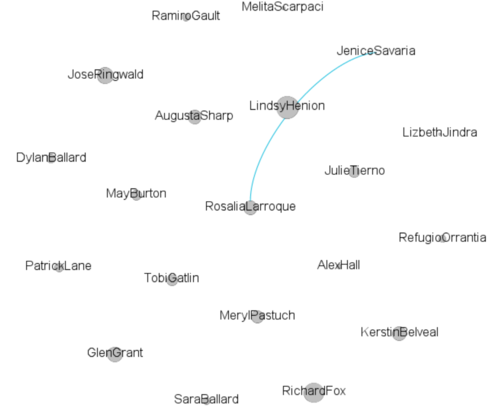
| + | <td><b> 4. Explore the company(4) </b> | ||
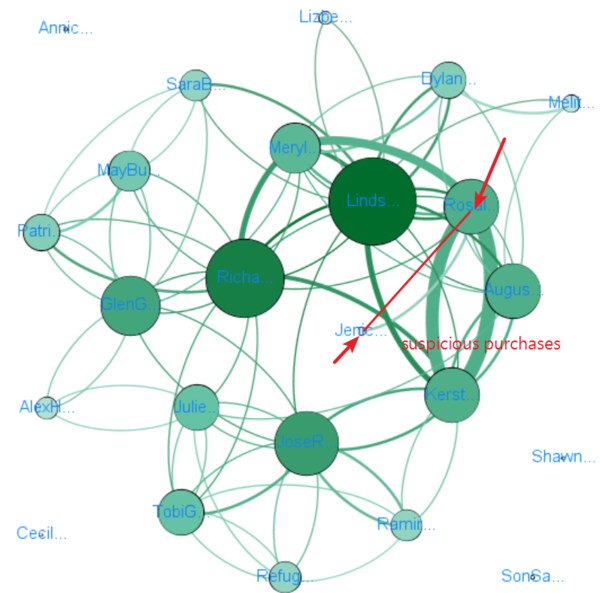
| + | <br>Pay attention to the suspicious purchases. There are only one record provided by insider. The transaction is made by ''JeniceSavaria'' and ''RosaliaLarroque''.It's interesting to find that '''no one else''' used to communicate with Jenice except Rosal. On the other hand, Rosal and Kerstin have close relationship.The transaction is happen on 2017-09-20. | ||
| + | </td> | ||
| + | <td>[[File:YzcSus3.png|600px|center]]</td> | ||
| + | </tr> | ||
| + | <tr> | ||
| + | <td><b> 5. Explore the company(5) </b> | ||
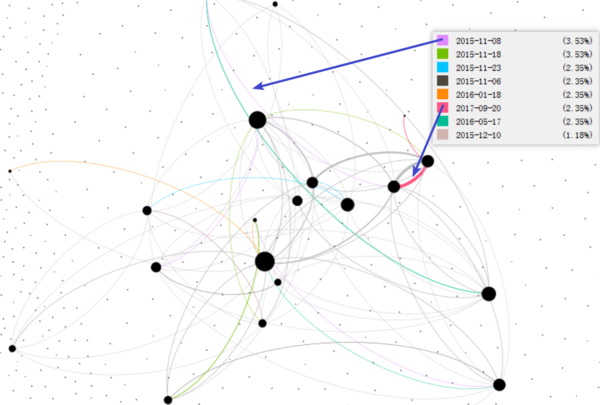
| + | <br>Most records are recorded in 2015-11. It seems that something suspicious happen during the period. | ||
| + | </td> | ||
| + | <td>[[File:YzcSus4.png|600px|center]]</td> | ||
| + | </tr> | ||
| + | </table> | ||
| + | ===Part3=== | ||
| + | <br> | ||
| + | <table border='1'> | ||
| + | <tr> | ||
| + | <th>Insights</th> | ||
| + | <th>Visualization</th> | ||
| + | </tr> | ||
| + | <tr> | ||
| + | <td><b> 1. Explore the suspicious group(1) </b> | ||
| + | <br>Three pictures represent the structure of suspicious group from 2015 to 2017. It's clear that there is obvious change over time. The central of each year is quite different. However, Richa must be important.It seems that there are more centrals in 2015. On the other hand, the trend of concentration of power is obvious. | ||
| + | </td> | ||
| + | <td>[[File:YzcSus5-1.png|200px]]</td> | ||
| + | <td>[[File:YzcSus5-2.png|200px]]</td> | ||
| + | <td>[[File:YzcSus5-3.png|200px]]</td> | ||
| + | </tr> | ||
| + | </table> | ||
| + | <br> | ||
| + | <table border='1'> | ||
| + | <tr> | ||
| + | <th>Insights</th> | ||
| + | <th>Visualization</th> | ||
| + | </tr> | ||
| + | <tr> | ||
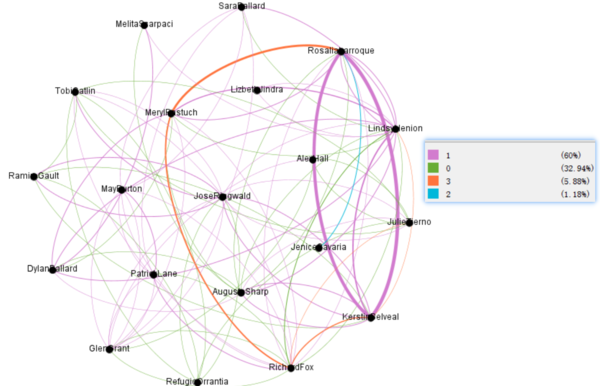
| + | <td><b> 2. Explore the suspicious group(2) </b> | ||
| + | <br>'''2 :purchase.''' | ||
| + | <br> '''3 :meetings.''' | ||
| + | <br> ''' 1 :emails.''' | ||
| + | <br> '''4 :calls''' | ||
| + | </td> | ||
| + | <td>[[File:YzcSus6.png|600px]]</td> | ||
| + | </tr> | ||
| + | </table> | ||
| + | <br> | ||
| + | <table border='1'> | ||
| + | <tr> | ||
| + | <th>Visualization</th> | ||
| + | <th>Visualization</th> | ||
| + | </tr> | ||
| + | <tr> | ||
| + | <td><b>[[File:YzcSus6-1.png|500px]] </b> | ||
| + | <br> | ||
| + | </td> | ||
| + | <td>[[File:YzcSus6-2.png|500px]]</td> | ||
| + | </tr> | ||
| + | <tr> | ||
| + | <td><b>[[File:YzcSus6-3.png|500px]] </b> | ||
| + | <br> | ||
| + | </td> | ||
| + | <td>[[File:YzcSus6-4.png|500px]]</td> | ||
| + | </tr> | ||
| + | </table> | ||
| + | |||
| + | '''The communication structure of the company is shown above.''' | ||
| + | |||
| + | ===Part4=== | ||
| + | |||
| + | <br> | ||
| + | <table border='1'> | ||
| + | <tr> | ||
| + | <th>Insights</th> | ||
| + | <th>Visualization</th> | ||
| + | </tr> | ||
| + | <tr> | ||
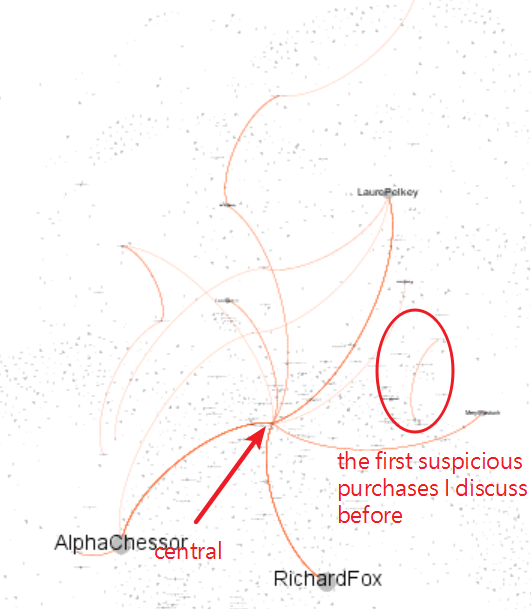
| + | <td><b> 1. Are there any other suspicious purchases? </b> | ||
| + | <br>The insider has provided a list of purchases that might indicate illicit activity elsewhere in the company.After adding the other_suspicious_purchases.csv to our data set, I might find any other instances of suspicious activities in the company. The suspicious activities must follow similar rule. | ||
| + | </td> | ||
| + | <td>[[File:YzcQ4-1.png|600px]]</td> | ||
| + | </tr> | ||
| + | <tr> | ||
| + | <td><b> 2. Are there any other suspicious purchases?(2) </b> | ||
| + | <br>The transaction between ''TrevorWebb'' and ''TyreeBarrenenhe'' is similar with the first group which insider provided. | ||
| + | </td> | ||
| + | <td>[[File:YzcQ4-2.png|600px]]</td> | ||
</tr> | </tr> | ||
Latest revision as of 02:11, 9 July 2018
|
|
|
|
|
Viz & Insights
part1
| Insights | Visualization |
|---|---|
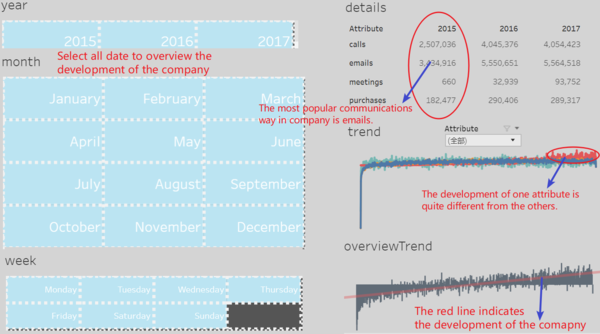
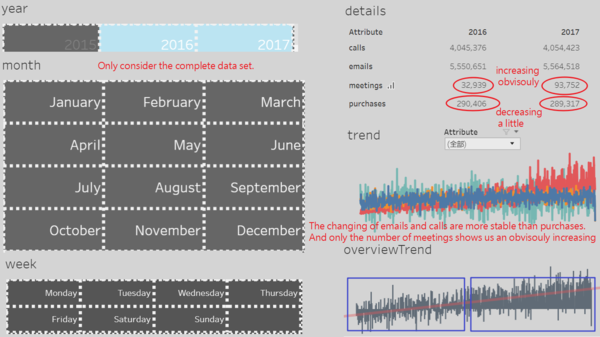
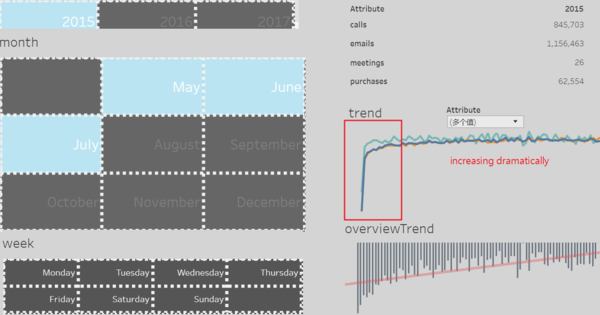
| 1. Overview the development of company
|
|
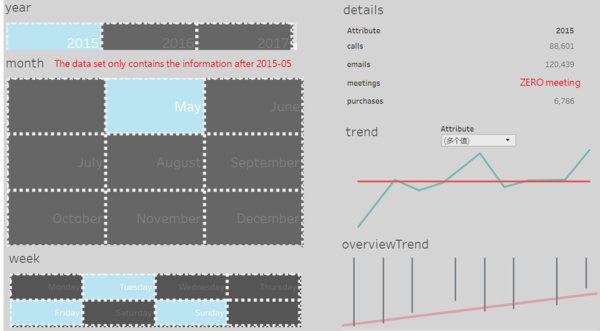
| 2. Overview the development of company(2)
|
|
| 3. Overview the development of company(3)
|
|
| 4. Overview the development of company(4)
|
Part2
| Insights | Visualization |
|---|---|
| 1. Explore the company
|
|
| 2. Explore the company(2)
|
|
| 3. Explore the company(3)
|
|
| 4. Explore the company(4)
|
|
| 5. Explore the company(5)
|
Part3
| Insights | Visualization |
|---|---|
| 2. Explore the suspicious group(2)
|
 |
| Visualization | Visualization |
|---|---|
|
 |
|
 |
The communication structure of the company is shown above.
Part4